Atomic Email Hunter 15.20.0.485 + License Key Free Download 2024
Atomic Email Hunter 15.20.0.485 is a strong email scratching and extraction instrument created by AtomPark Programming Inc. It is intended to assist clients with building designated email records by extricating email addresses from sites, web indexes, and other internet-based sources. Atomic Email Hunter is principally known for its email extraction capacities. The product can filter sites, web indexes, and other internet-based stages to gather email addresses. This is especially helpful for organizations and advertisers seeking to construct designated email records for their missions.
Clients can characterize explicit inquiry rules to precisely focus on their crowd. Atomic Email Hunter permits clients to look for email trends in light of watchwords, spaces, or different boundaries, guaranteeing that the removed messages line up with the client’s targets. The product uses multi-strung handling to improve proficiency. This implies that Atomic Email Hunter can all the while cycle different pages, speeding up the email extraction interaction and saving clients time.
Atomic Email Hunter incorporates flawlessly with well-known web search tools, permitting clients to remove email addresses from query items. This element empowers clients to target explicit enterprises, specialties, or districts in light of their hunt questions. To keep up with the nature of removed email records, Atomic Email Hunter incorporates an underlying email verifier. This component browses the legitimacy of email addresses, diminishing the probability of sending messages to non-existent or idle records and further developing deliverability rates.
Atomic Email Hunter + Serial Key
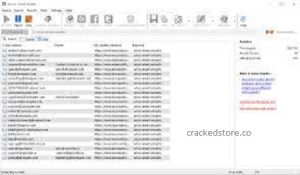
Atomic Email Hunter + Serial Key When the email addresses are gathered, Atomic Email Hunter gives different product choices. Clients can trade the information in various configurations, for example, CSV or TXT documents, making it simple to bring the email records into other advertising apparatuses or stages. The product includes an easy-to-use interface that is instinctive and simple to explore. This makes Atomic Email Hunter open to clients with fluctuating degrees of specialized skill, permitting them to use its strong capacities without a lofty expectation to learn and adapt.
To improve client protection and stay away from IP obstructing, Atomic Email Hunter upholds the utilization of intermediaries. Clients can design the product to make demands through intermediary servers, giving an additional layer of obscurity during the email extraction process. Atomic Email Hunter is effectively kept up with and refreshed by AtomPark Programming. Customary updates guarantee similarity with the most recent web advancements and web crawler calculations. Also, the product is upheld by client service, offering help to clients who might experience issues or have requests about its highlights.
Atomic Email Hunter is a flexible device for organizations and advertisers trying to construct designated email records. Its strong email extraction capacities, designated search standards, and easy-to-understand interface make it an important resource for those hoping to smooth out their email-promoting endeavors and interface with a particular crowd. In any case, clients ought to be aware of lawful and moral contemplations while utilizing email extraction devices to guarantee consistency with protection guidelines and terms of administration on different web-based stages.
Atomic Email Hunter + Registration Key
Atomic Email Hunter + Registration Key gives adjustable hunt channels, permitting clients to tweak their inquiries in light of boundaries, for example, the profundity of the pursuit, the kind of messages to remove (e.g., from pages, message records, or different sources), and the consideration or prohibition of explicit spaces. This degree of customization empowers clients to tailor their inquiries to meet explicit standards and focus on a more exact crowd. The product can slither through the substance of sites and follow connections to find email tends to be implanted in the site’s pages. This creeping highlight is useful for removing messages from complex sites or registries where direct pursuit questions may not be adequate.
Clients can perform email extraction given explicit catchphrases applicable to their specialty or industry. Atomic Email Hunter looks for email addresses related to the predetermined catchphrases, assisting clients with building email records that line up with their business or showcasing targets. Atomic Email Hunter is intended to deal with enormous-scope email extraction errands. Whether clients are hoping to fabricate broad email records or focus on a particular section inside an enormous data set, the product’s versatility makes it a reasonable instrument for a scope of ventures.
Atomic Email Hunter permits clients to remove email addresses from neighborhood records or disconnected sources. This component is significant when clients have existing datasets or documents containing potential email contacts that they need to integrate into their missions. Notwithstanding sites and web crawlers, Atomic Email Hunter can separate email addresses from online entertainment stages. This component is helpful for organizations hoping to associate with expected clients or partners dynamic on stages like LinkedIn or Twitter.
Key Features:
- Atomic Email Hunter succeeds in separating email addresses from different sources, including sites, web search tools, and online catalogs.
- Clients can perform designated look-throughs given explicit watchwords, permitting them to zero in on specific enterprises, specialties, or interests.
- The product can creep through site content and follow joins, gathering email tends to be implanted in the pages.
- Atomic Email Hunter gives adjustable inquiry channels, empowering clients to refine their ventures in light of boundaries, for example, the profundity of the hunt and the kinds of messages to extricate.
- The device utilizes multi-strung handling, permitting concurrent extraction from numerous site pages, which improves proficiency and paces up the cycle.
- Clients can trade the gathered email in different configurations, for example, CSV or TXT documents, making it simple to coordinate the information into other promoting devices or stages.
- To guarantee the nature of the extricated email records, Atomic Email Hunter includes an inherent email verifier that browses the legitimacy of email addresses.
More Features:
- Clients can design intermediary settings to improve protection, keep away from IP impeding, and guarantee the smooth activity of the email extraction process.
- Atomic Email Hunter can remove email addresses from web-based entertainment stages, permitting clients to interface with expected clients or colleagues dynamic on stages like LinkedIn or Twitter.
- The product upholds the extraction of email addresses from neighborhood documents or disconnected sources, furnishing adaptability for clients with existing datasets.
- The device upholds intermittent cleaning of email data sets, empowering clients to eliminate obsolete or invalid email locations to keep up with list quality.
- Atomic Email Hunter normally includes an easy-to-understand interface that works with usability and route for clients with shifting degrees of specialized mastery.
- The product is effectively kept up with customary updates to guarantee similarity with the most recent web innovations and web crawler calculations. Client service is frequently accessible to help clients with requests or issues.
What’s New?
- Finds Facebook addresses
- Letterbox module
- LinkedIn module
- Recuperates a wide range of data
- Peruse playback on Facebook
- New atomic pioneer
- High-level national acknowledgment
- Anatomic pioneer extractor
System Requirements:
- Windows 10 latest OS from Microsoft
- Windows 7 is the latest version of Microsoft’s operating
- XP (Windows XP Professional)
- Processor: 800 MHz CPU
- RAM: 256 MB
- HDD: 70 MB
- Connection to the Internet
License Key:
- Q1W2E3R5TYU7I8O90P1QWI
- E3RT5YU7I8O9P0O9I8U7Y6T
- 4R3E2W1QW2E3R4T5Y6U78I
- 9OP0O9I8U76YT54RE32W1QI
Activation Key:
- W2E3R4T5Y6U78I9O0PP0O9I
- 8U7Y6T54RE32W1QW2E3RT5
- YU7I8O9P0Q1W2E3R4T5Y6UI
- I8O9P0Q1W2E3R4T5Y6U7I8O
How To Install?
- First of all, download Atomic Email Hunter from the below link.
- Run this document and save it in the C registry
- Then, at that point, close it and create Keys
- Duplicate everything and glue it
- At long last, the full variant is dynamic at this point.